Loss Exceeds $1 Million, Fake Zoom Meeting Phishing Analysis
Original Title: "Seeing is Not Believing | Analysis of Fake Zoom Meeting Phishing"
Original Source: SlowMist Technology
Background
Recently, several users on platform X reported a phishing attack method that disguised itself as a Zoom meeting link. One victim clicked on a malicious Zoom meeting link, which led to the installation of malware, resulting in the theft of encrypted assets and losses amounting to millions of dollars. In this context, the SlowMist security team conducted an analysis of this phishing event and attack method, and traced the hacker's fund flow.
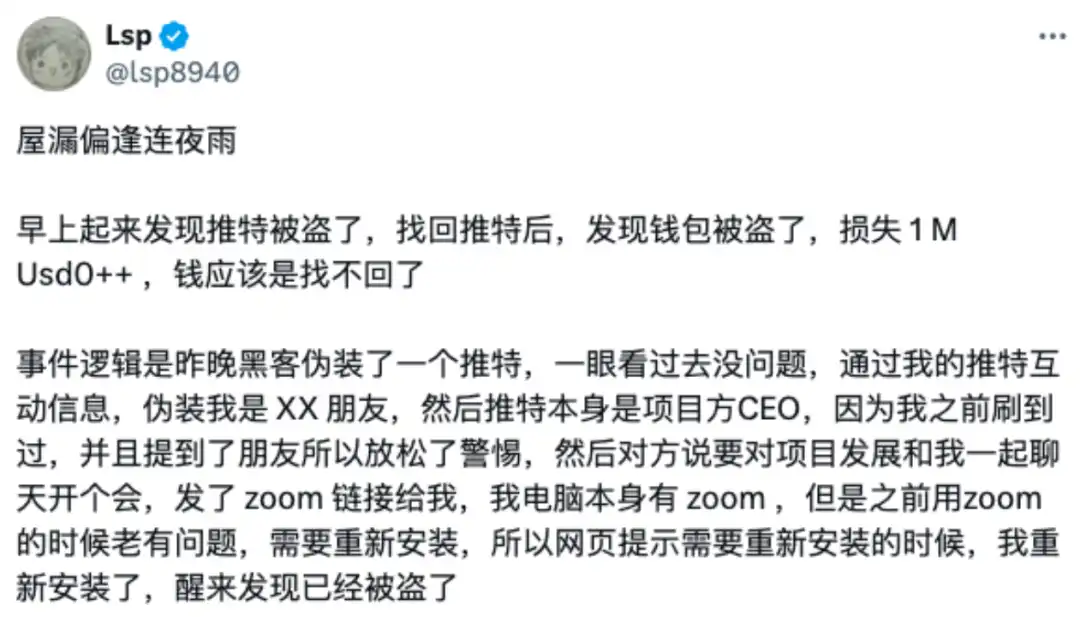
(https://x.com/lsp8940/status/1871350801270296709)
Phishing Link Analysis
The hacker used a domain name like "app[.]us4zoom[.]us" to disguise itself as a legitimate Zoom meeting link. The page closely resembled a real Zoom meeting, and when users clicked the "Start Meeting" button, it triggered the download of a malicious installer package instead of starting the local Zoom client.

Through probing the above domain, we discovered the hacker's monitoring log address (https[:]//app[.]us4zoom[.]us/error_log).

Upon decryption, it was found that this was a log entry when the script attempted to send a message via the Telegram API, using the Russian language.

The site was deployed online 27 days ago, and the hacker may be Russian. Since November 14th, they have been seeking targets and then monitoring through the Telegram API to see if any targets click the download button on the phishing page.

Malware Analysis
The malicious installer package's filename is "ZoomApp_v.3.14.dmg." Below is the interface opened by this Zoom phishing software, which prompts users to execute the ZoomApp.file malicious script in Terminal and also prompts users to enter their local password during the execution process.

Below is the execution content of this malicious file:

Upon decoding the above content, it was found to be a malicious osascript script.

Further analysis revealed that the script searches for a hidden executable file named ".ZoomApp" and runs it locally. We conducted disk analysis on the original installation package "ZoomApp_v.3.14.dmg" and indeed found that the package was hiding an executable file named ".ZoomApp".

Malicious Behavior Analysis
Static Analysis
We uploaded this binary file to a threat intelligence platform for analysis, and the file was identified as malicious.

(https://www.virustotal.com/gui/file/e4b6285e183dd5e1c4e9eaf30cec886fd15293205e706855a48b30c890cbf5f2)
Through static disassembly analysis, the following is the entry code of this binary file, used for data decryption and script execution.

Below is the data section, where it can be observed that most of the information has been encrypted and encoded.

Upon decrypting the data, it was found that this binary file ultimately executes a malicious osascript script (complete decryption code shared at: https://pastebin.com/qRYQ44xa), which collects information from the user's device and sends it to a backend.
Below is a section of the code enumerating different plugin ID paths.

Below is a section of the code reading KeyChain information from the computer.

The malicious code, after collecting system information, browser data, encrypted wallet data, Telegram data, Notes data, and Cookie data, compresses them and sends them to a hacker-controlled server (141.98.9.20).

Since the malware prompts users to enter their password during runtime and subsequent malicious scripts also collect KeyChain data from the computer (potentially containing various passwords saved by the user on the computer), the hacker, upon collection, will attempt to decrypt the data to obtain sensitive information such as the user's wallet mnemonic phrase and private key, thereby stealing the user's assets.
Analysis shows that the IP address of the hacker's server is located in the Netherlands and has been flagged as malicious by a threat intelligence platform.

(https://www.virustotal.com/gui/ip-address/141.98.9.20)
Dynamic Analysis
By dynamically executing this malicious program in a virtual environment and analyzing the process, the following image shows the process monitoring information of the malicious program collecting local data and sending data to the backend.


MistTrack Analysis
We used the on-chain tracking tool MistTrack to analyze the hacker address provided by the victim: 0x9fd15727f43ebffd0af6fecf6e01a810348ee6ac. The hacker address has profited over $1 million, including USD0++, MORPHO, and ETH; of which, USD0++ and MORPHO were exchanged for 296 ETH.
According to MistTrack, the hacker address has received small amounts of ETH from address 0xb01caea8c6c47bbf4f4b4c5080ca642043359c2e, presumably as a fee for the hacker address. The address (0xb01c) only has one source of income but has sent out small amounts of ETH to nearly 8,800 addresses, appearing to be a "platform specifically providing fees."

Filter out the outgoing addresses from this address (0xb01c) that have been flagged as malicious, associated with two phishing addresses, one of which is marked as the Pink Drainer, and further analyze these two phishing addresses, with funds mostly transferred to ChangeNOW and MEXC.

Next, analyze the outgoing transactions of the stolen funds, where a total of 296.45 ETH was transferred to a new address 0xdfe7c22a382600dcffdde2c51aaa73d788ebae95.

The first transaction from the new address (0xdfe7) was in July 2023, involving multiple chains, and the current balance is 32.81 ETH.

The main ETH outflow paths from the new address (0xdfe7) are as follows:
· 200.79 ETH -> 0x19e0…5c98f
· 63.03 ETH -> 0x41a2…9c0b
· 8.44 ETH -> Exchanged for 15,720 USDT
· 14.39 ETH -> Gate.io

The subsequent outflows from the expanded addresses are associated with multiple platforms such as Bybit, Cryptomus.com, Swapspace, Gate.io, MEXC, and are related to multiple addresses marked by MistTrack as Angel Drainer and Theft. Additionally, there is currently 99.96 ETH remaining in the address 0x3624169dfeeead9f3234c0ccd38c3b97cecafd01.

The USDT transaction trace from the new address (0xdfe7) is also extensive, with transfers to platforms such as Binance, MEXC, FixedFloat, and others.

Summary
The phishing method shared this time is where hackers disguise themselves as a legitimate Zoom meeting link, tricking users into downloading and executing malicious software. This malware usually has multiple harmful functions such as collecting system information, stealing browser data, and obtaining cryptocurrency wallet information, which is then transmitted to a server controlled by the hacker. These types of attacks often combine social engineering and trojan horse attack techniques, making users vulnerable to falling victim with slight carelessness. The SlowMist Security Team advises users to carefully verify before clicking on any meeting links, avoid executing software and commands from unknown sources, install antivirus software, and keep it updated regularly. For more security insights, it is recommended to read the SlowMist Security Team's "Blockchain Dark Forest Self-Rescue Handbook": https://github.com/slowmist/Blockchain-dark-forest-selfguard-handbook/blob/main/README_CN.md.
You may also like

Ray Dalio's new article: The world is entering a war cycle

IOSG: When Fintech Meets Crypto Native: The Next Decade of Digital Finance

They knew in advance that Trump would tweet about a ceasefire, entered with $20k, and exited with $400k.

The biggest bottleneck in DeFi development

CZ Memoir Released: Reveals a Large Amount of Industry Insider Information, Prompting Intense Rebuttal from Xu Mingxing

a16z: After securities are on the blockchain, why will intermediary institutions be replaced by code?

XRP Tokyo Is Here: What We Learn and What’s Next for XRP Price
Key Takeaways: Ripple’s 2025 XRP Tokyo event highlights a projected $33 trillion on-chain stablecoin volume by 2026. Significant…

Solana’s Future: Navigating the $285M Hack, Rug Pulls, and Milei Libra Scandal
Key Takeaways: Multiple Crises: Solana faces a $285 million hack, allegations of rug pulls, and the Milei Libra…

BTC USD Faces Tension: Markets React to Trump’s Dire Warning
Key Takeaways: Bitcoin’s price drops sharply below $70,000 amid geopolitical tensions, playing off Trump’s dramatic 8 PM ultimatum…

Bitcoin Price Surge: Ceasefire Sparks Optimism Hits $71K
Key Takeaways: After the US-Iran ceasefire announcement, Bitcoin surged beyond $71,000, marking its highest in a month. A…

Ethereum Price Forecast: Record $180 Billion Stablecoin Supply Marks Buyers’ Return
Key Takeaways: Ethereum’s stablecoin supply has surged to a record $180 billion, marking a 150% increase over the…

Emerging Evidence Links Argentina’s Milei to LIBRA Crypto Scandal
Key Takeaways: Evidence unveiled by Argentina’s federal prosecutors links President Javier Milei to the LIBRA token through call…

US Spot Bitcoin ETFs See Surge as BTC Nears $70K; LiquidChain and Layer-3 DeFi Rise
Key Takeaways: U.S. spot Bitcoin ETFs absorbed $471 million in a single day, moving BTC closer to the…

Bitcoin Price Prediction: Decoupling from Tech Stocks, Shaped by Geopolitics and AI Turmoil
Key Takeaways: Bitcoin is decoupling from tech stocks as geopolitical tensions and AI crises reshape the market, currently…

Chaos Labs Departure Leaves Aave Without Risk Management Amidst Governance Conflict
Key Takeaways: Aave, with a $50 billion TVL, is currently operating without a risk manager due to Chaos…

Grayscale Ethereum ETF Staking: A New Catalyst for $5,700?
Key Takeaways: Grayscale’s Ethereum Staking ETF introduces a yield-bearing structure that could significantly reshape investor sentiment. Ethereum’s price…

Polygon Crypto Enhances Finality Through the Giugliano Hardfork
Key Takeaways: Polygon’s Giugliano hardfork is operational on the mainnet, effectively reducing transaction finality by 2 seconds. The…

Senate’s Three-Week Deadline: Ripple XRP and the CLARITY Act’s Critical Moment
Key Takeaways: The Senate Banking Committee’s decision on the CLARITY Act in late April could define XRP’s future…

